What Makes Securoty Badges No Longer Read
Security conferences are a great place to learn about the latest hacking tricks, tools and exploits, just they also remind usa of important stuff that was shown to be hackable in previous years yet never actually got stock-still. Perhaps the best example of this at last calendar week'due south annualDefCon security briefing in Las Vegas came from hackers who built on enquiry showtime released in 2010 to show simply how trivial it nevertheless is to read, modify and clone nearHID cards — the rectangular white plastic "smart" cards that organizations worldwide distribute to employees for security badges.

HID iClass proximity card.
Nearly four years ago, researchers at the Chaos Communication Congress (CCC), a security conference in Berlin, released a paper (PDF) demonstrating a serious vulnerability in smart cards made past Austin, Texas-based HID Global, by far the largest manufacturer of these devices. The CCC researchers showed that the bill of fare reader device that HID sells to validate the data stored on its and so-new line of iClass proximity cards includes the principal encryption key needed to read data on those cards.
More importantly, the researchers proved that anyone with physical access to 1 of these readers could extract the encryption key and use it to read, clone, and modify information stored on any HID cards made to work with those readers.
At the time, HID responded by modifying future models of carte du jour readers then that the firmware stored within them could not be then easily dumped or read (i.e., the company removed the external serial interface on new readers). But according to researchers, HID never changed the master encryption key for its readers, probable because doing so would require customers using the product to change or replace all of their readers and cards — a costly proposition by whatever measure out given HID's huge marketplace share.
Unfortunately, this means that anyone with a modicum of hardware hacking skills, aneBay account, and a upkeep of less than $500 tin can catch a copy of the chief encryption central and create a portable system for reading and cloning HID cards. At least, that was the gist of the DefCon talk given last week by the co-founders of Lares Consulting, a visitor that gets hired to test clients' physical and network security.
Lares' Joshua Perrymon and Eric Smith demonstrated how an HID parking garage reader capable of reading cards upward to three anxiety away was purchased off of eBay and modified to fit inside of a common backpack. Wearing this haversack, an assailant looking to gain admission to a building protected by HID's iClass cards could obtain that access but by walking up to a employee of the targeted organization and request for directions, a light of a cigarette, or some other pretext.
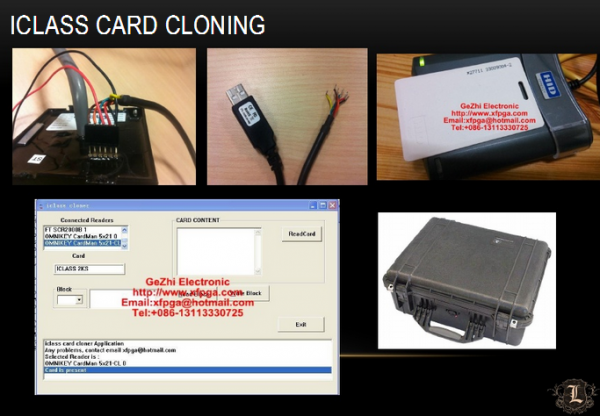
Card cloning gear fits in a briefcase. Prototype: Lares Consulting.
Perrymon and Smith noted that, thanks to software tools available online, it's piece of cake to take carte du jour data gathered past the mobile reader and encode information technology onto a new bill of fare (also broadly available on eBay for a few pennies apiece). Worse still, the attacker is then as well able to gain access to areas of the targeted facility that are off-limits to the legitimate owner of the card that was cloned, because the ones and zeros stored on the bill of fare that specify that access level likewise can exist modified.
Smith said he and Perrymon wanted to revive the result at DefCon to raise awareness about a widespread vulnerability in physical security. HID did not respond to multiple requests for comment.
"Until recently, no one has really demonstrated properly what the hazard is to a business concern here," Smith said. "SCADA installations, hospitals, airports…a lot of them utilize HID cards because HID is the leader in this space, but they're using compromised engineering science. Your bill of fare might not have data centre or HR access merely I can get into those places within your organisation simply by coming up to some employee standing outside the building and aimless a light off of him."
Organizations that are vulnerable have several options. Probably the cheapest involves the use of some type of sleeve for the smart cards. The wireless communications technology that these cards use to transmit information — chosen radio-frequency identification or RFID – can be blocked when not in use by storing the fundamental cards inside a special RFID-shielding sleeve or wallet. Of course, organizations can replace their readers with newer (perhaps not-HID?) technology, and/or add together biometric components to card readers, but these options could get pricey in a hurry.
A re-create of the slides from Perrymon and Smith's DefCon talk is available here.
Source: https://krebsonsecurity.com/2014/08/how-secure-is-your-security-badge/
0 Response to "What Makes Securoty Badges No Longer Read"
Enregistrer un commentaire